Overview
Created a tool to make learning about and exploiting buffer overflow (“buffer overrun”) attacks easier by removing additional required software using only basic HTML and JavaScript.
Tool is available at: https://projects.jason-rush.com/tools/buffer-overflow-eip-offset-string-generator/
Context
I have been interested in security (digital or physical) since I was very young, and I have spent a bit of time learning how to exploit software so I can learn how to more readily secure the code I write. The idea to create this project came about while learning how buffer overflows function, and how they are exploited. Most of the process of exploiting a buffer overflow (at least in simple examples used in training) can be done in your head, a command or two run form a terminal, and copying and pasting pre-created shellcode. The one step I consistently had to have a separate piece of software for is verifying how long of an offset is needed before you can insert your shellcode address.
Typically, you would install a pair of scripts (pattern_create and pattern_offset) via Metasploit (though a few other sources were available that also required additional software be installed). You would use pattern_create to generate a string where every 4-character combination is unique, and pass that string through the application you want to exploit which would crash as the EIP register was set with an “invalid” value. The “invalid” value was caused by a buffer overflow causing 4 consecutive bytes of our generated string to be loaded into the EIP register. If we get the value of EIP when it crashed (typically by using a debugger, such as GDB), we would then pass the string to pattern_offset which would tell us how many bytes in we need to place the address where our shellcode will be.
I quickly realized I usually didn’t want to install the entire Metasploit module just for these two scripts, and they were simple enough I should be able to easily recreate them in any other language I wanted.
Project Overview
I decided I wanted my version of these scripts to be web-based so no software is required (it’s very rare I run into a desktop or laptop without a browser installed), and decided they should be JavaScript-based since that would mean a user could save the tool (webpage) and subsequently use them offline while still saving a substantial amount of space compared to installing Metasploit.
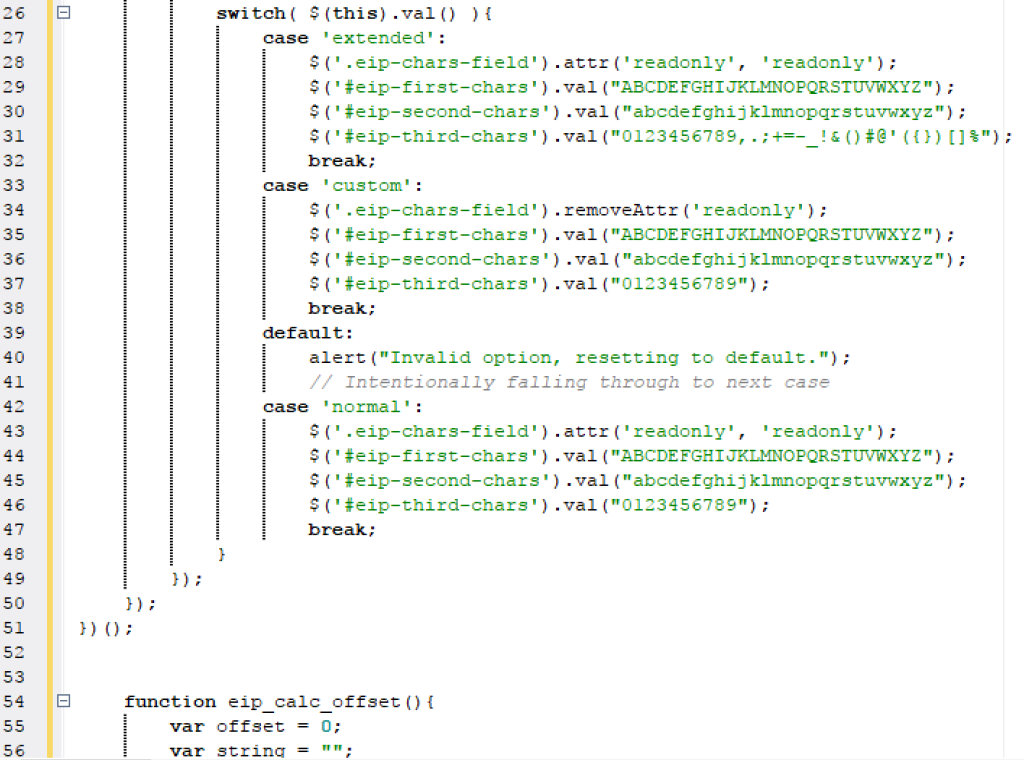
While my version of these tools didn’t need to be fully compatible with the originals, I aimed to support that compatibility as well as extending functionality by allowing a few ways to customize the tools depending on requirements.
Services Provided
- Replicated algorithms used to generate the initial string, and calculate position in the string
- Added additional functionality to extend maximum string length (due to mathematical, not technological limitations)
- Added additional functionality to customize input strings for cases where certain standard characters may not be allowed
Impact
While I haven’t had the time to play with buffer overflow exploits in quite some time, this tool is my most popular tool at the time of this post. Most users reach this tool through various search engines, but there are a few hacking-related websites that link to it as well as a Taiwanese university that seems to be linking to the page through their elearning site.